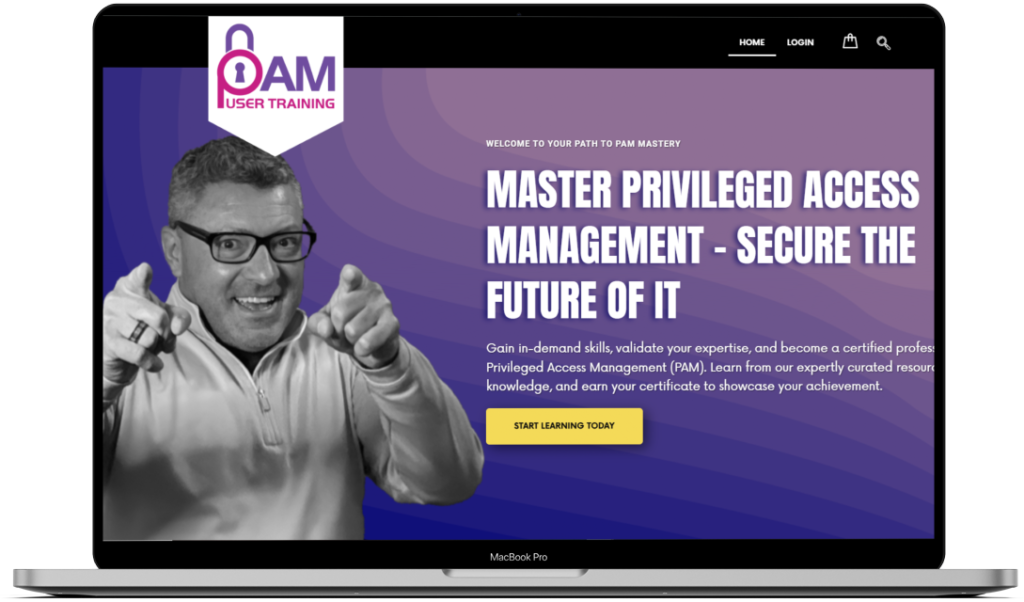
Privileged access management policy
Policies for privileged access management, or PAM, are fundamental frameworks that specify how a company manages and keeps an eye on access to its most important systems and private information. These policies lay out the rules and processes for giving, controlling, and removing privileged access, making sure that only people with the proper authorization can carry out important administrative duties. A PAM policy’s objective is to reduce the risks connected to privileged accounts, which are popular targets for cybercriminals because of their broad access privileges. Organizations can greatly improve their security posture and safeguard their assets from possible intrusions by putting in place a strong PAM strategy.

YouTube
Just in Time Permissions Explained #Delinea #PAM #CyberSecurity
A thorough PAM policy consists of various essential elements. It first establishes the requirements for who is eligible for privileged access and when. This entails a rigorous screening procedure to guarantee that only reliable and competent people are granted access.
Secondly, the policy delineates the concept of least privilege, guaranteeing that users possess the bare minimum of access required to execute their responsibilities. By doing this, the possible harm from an account compromise is reduced.
The policy also requires privileged accounts to be regularly reviewed and audited in order to quickly identify any irregularities or unlawful activity.
To uphold these standards and provide ongoing supervision, automated instruments and procedures are frequently used. Additionally, a clear PAM policy takes care of the requirement for strong authorization and authentication systems. Access to privileged accounts usually requires multi-factor authentication (MFA), which adds an additional degree of protection.
The policy also mandates the use of safe techniques, including hardware security modules (HSMs) or encrypted vaults, for handling and storing privileged credentials. It also contains protocols for tracking and recording privileged access operations, guaranteeing that thorough documentation is maintained for compliance and forensic analysis needs. Organizations that enforce strict PAM policies not only protect their vital systems but also show that they are committed to cybersecurity best practices, which can build trust among stakeholders and customers.
YouTube
OATH OTP MFA Explained: Easy Setup Guide for Stronger Security
About Me
Bert Blevins is a distinguished technology entrepreneur and educator who brings together extensive technical expertise with strategic business acumen and dedicated community leadership. He holds an MBA from the University of Nevada Las Vegas and a Bachelor’s degree in Advertising from Western Kentucky University, credentials that reflect his unique ability to bridge the gap between technical innovation and business strategy.

As a Certified Cyber Insurance Specialist, Mr. Blevins has established himself as an authority in information architecture, with particular emphasis on collaboration, security, and private blockchain technologies. His comprehensive understanding of cybersecurity frameworks and risk management strategies has made him a valuable advisor to organizations navigating the complex landscape of digital transformation. His academic contributions include serving as an Adjunct Professor at both Western Kentucky University and the University of Phoenix, where he demonstrates his commitment to educational excellence and knowledge sharing. Through his teaching, he has helped shape the next generation of technology professionals, emphasizing practical applications alongside theoretical foundations.
In his leadership capacity, Mr. Blevins served as President of the Houston SharePoint User Group, where he facilitated knowledge exchange among technology professionals and fostered a community of practice in enterprise collaboration solutions. He further extended his community impact through director positions with Rotary International Las Vegas and the American Heart Association’s Las Vegas Chapter, demonstrating his commitment to civic engagement and philanthropic leadership. His specialized knowledge in process optimization, data visualization, and information security has proven instrumental in helping organizations align their technological capabilities with business objectives, resulting in measurable improvements in operational efficiency and risk management.
Mr. Blevins is recognized for his innovative solutions to complex operational challenges, particularly in the realm of enterprise architecture and systems integration. His consulting practice focuses on workplace automation and digital transformation, guiding organizations in the implementation of cutting-edge technologies while maintaining robust security protocols. He has successfully led numerous large-scale digital transformation initiatives, helping organizations modernize their technology infrastructure while ensuring business continuity and regulatory compliance. His expertise extends to emerging technologies such as artificial intelligence and machine learning, where he helps organizations identify and implement practical applications that drive business value.

As a thought leader in the technology sector, Mr. Blevins regularly contributes to industry conferences and professional forums, sharing insights on topics ranging from cybersecurity best practices to the future of workplace automation. His approach combines strategic vision with practical implementation, helping organizations navigate the complexities of digital transformation while maintaining focus on their core business objectives. His work in information security has been particularly noteworthy, as he has helped numerous organizations develop and implement comprehensive security frameworks that address both technical and human factors.
Beyond his professional pursuits, Mr. Blevins is an accomplished endurance athlete who has participated in Ironman Triathlons and marathons, demonstrating the same dedication and disciplined approach that characterizes his professional work. He maintains an active interest in emerging technologies, including drone operations and virtual reality applications, reflecting his commitment to staying at the forefront of technological advancement. His personal interests in endurance sports and cutting-edge technology complement his professional expertise, illustrating his belief in continuous improvement and the pursuit of excellence in all endeavors.